With the latest Windows 10 Insider build, new hidden features have been found that add long-awaited media controls to the volume flyout and a new settings page that shows a ‘What’s New’ section for the current Windows release.
As Microsoft developers work on new features for Windows 10, they hide them from being used by users. These features, though, can be enabled by the developers as needed for testing.
These hidden features can be enabled using tools like Mach2 or ViVe, but as they are still in-development and can cause Windows to not work properly. Due to this, it is strongly suggested that you only enable them in a virtual machine where you have a saved snapshot you can restore to if something goes wrong.
Below are the new upcoming and in development features found by Windows sleuth Albacore in the latest Windows 10 Insider build.
Flyout media controls coming to Windows 10
In the Windows 10 Insider preview build 19603, Microsoft is developing a new feature that adds media controls in the volume flyout.
As you can see from the image below, these media controls support Windows 10 music streaming applications such as Groove and Spotify and allow you to control the program directly from the flyout.
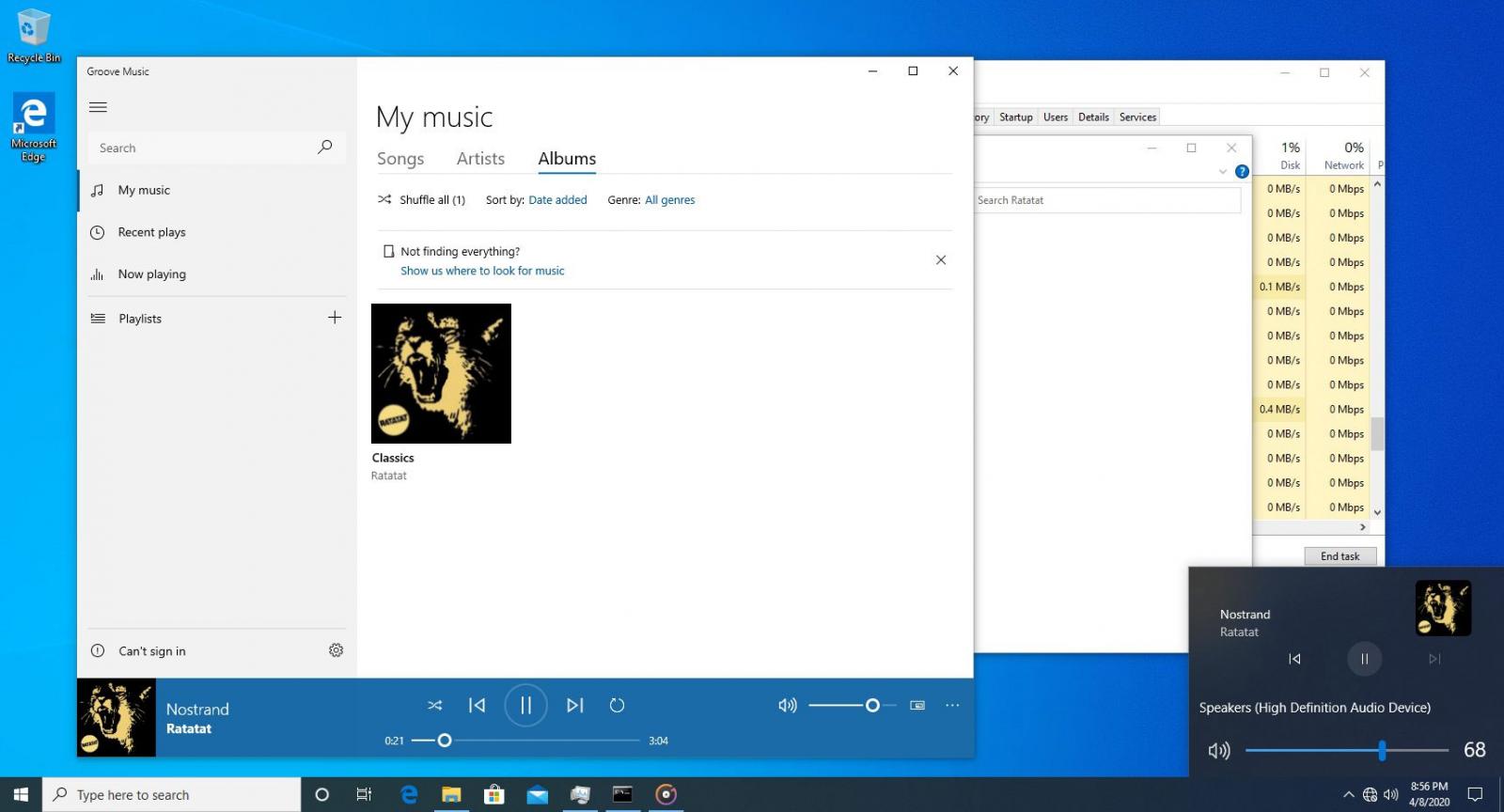
This feature can be enabled with mach2 using the commands:
mach2 enable 23403403 mach2 enable 23674478
WARNING: As previously stated, it is strongly advised that you do not enable this is on a production computer and only test in a virtual machine.
‘What’s New’ settings page shows off new features
Microsoft is adding a new ‘What’s New’ settings page that will list all the new features added to Microsoft with detailed instructions on how to use them.
When this hidden feature is enabled, it will add a ‘What’s New’ section under Settings > Update & Security as shown below.
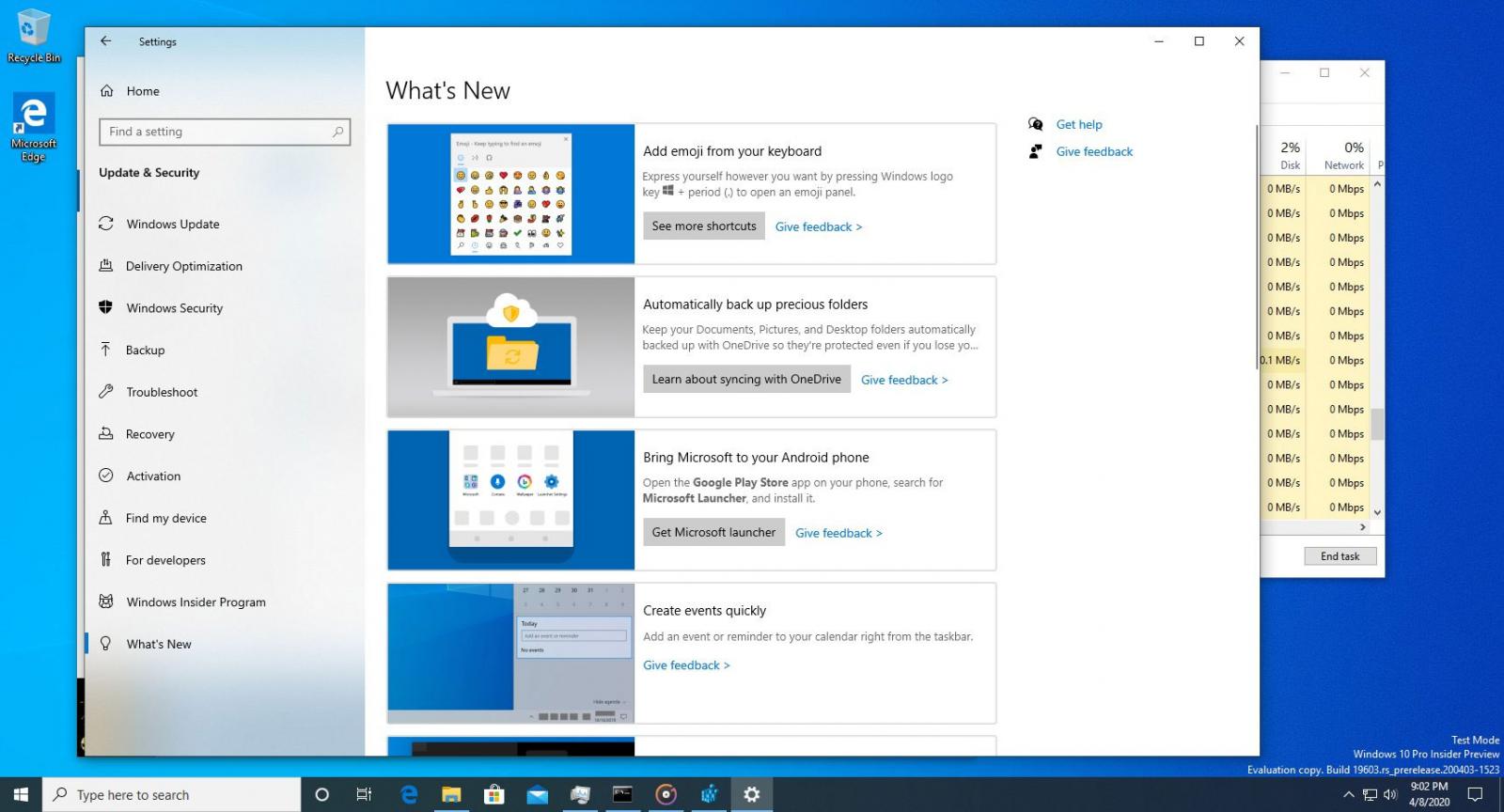
Hidden What’s New settings page
If you click on one of the feature boxes, a more detailed information panel will open that explains how you can use this feature.
This feature can be enabled with mach2 using the commands:
mach2 enable 20446796
WARNING: As previously stated, it is strongly advised that you do not enable this is on a production computer and only test in a virtual machine.