The EU has paved the way for all smartphones to be legally required to use a USB-C port for charging, a move that could be a headache for Apple, whose iPhone is the only main brand smartphone without this type of connection.
The EU’s agreement will apply from autumn 2024 for all smartphones sold in the bloc, a decision that could substantially impact Apple as the iPhone uses Apple’s lightning port for wired charging.
USB-C ports were introduced in Apple’s 12in MacBook model in 2015 and in the iPad Pro in late 2018, while other iPads have come with the port since 2020.
Some Apple users with devices featuring the lightning connector praise its “grip”, with some complaining that USB-C ports become loose over time.
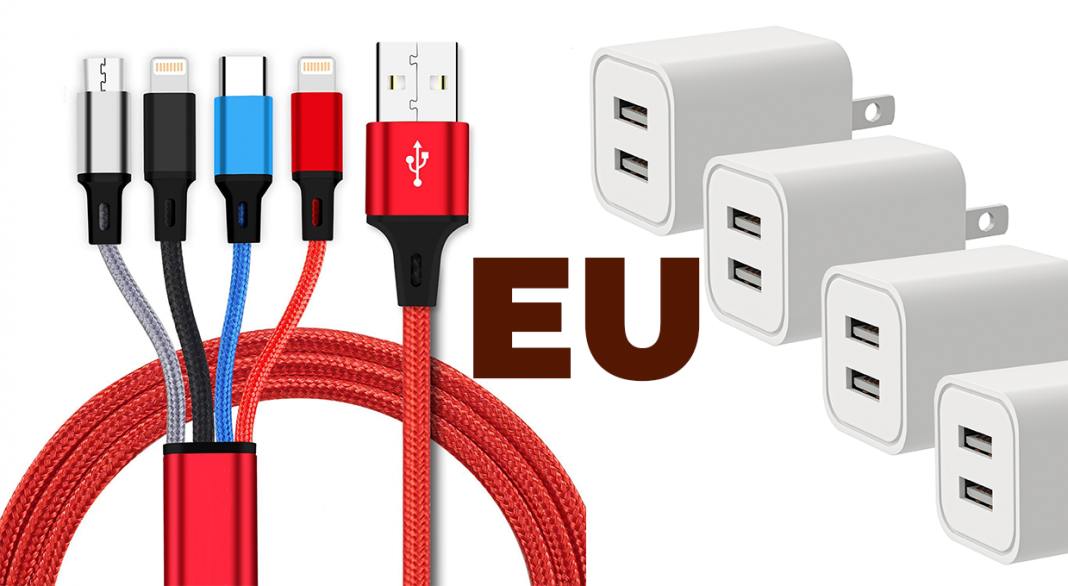
Others have expressed their desire to do away with their “dongle” bundles of adapters and replace them with a universal cable for all Apple products.
The EU said the rule change aims to reduce hassle for consumers as well as electronic waste, as it will enable consumers to use older chargers for new devices.
The rules will apply to “all small and medium-sized portable electronic devices”, which will include mobile phones, tablets, cameras, keyboards, speakers, headphones, headsets and earbuds. Laptops will have to be adapted to fit the requirements 40 months after they come into force.
The decision is yet to be approved by the European parliament and European Council, but is expected to be a formality.
European parliament spokesperson Alex Agius Saliba said: “Today we have made the common charger a reality in Europe.
“European consumers were long frustrated with multiple chargers piling up with every new device. Now they will be able to use a single charger for all their portable electronics.
“We are proud that laptops, e-readers, earbuds, keyboards, computer mice and portable navigation devices are also included, in addition to smartphones, tablets, digital cameras, headphones and headsets, handheld video game consoles and portable speakers.