Google is testing a dark mode for desktop search, Google confirmed to The Verge. If the test has rolled out to you and your system is set to dark mode, the background of Google’s search pages will be a very dark gray.
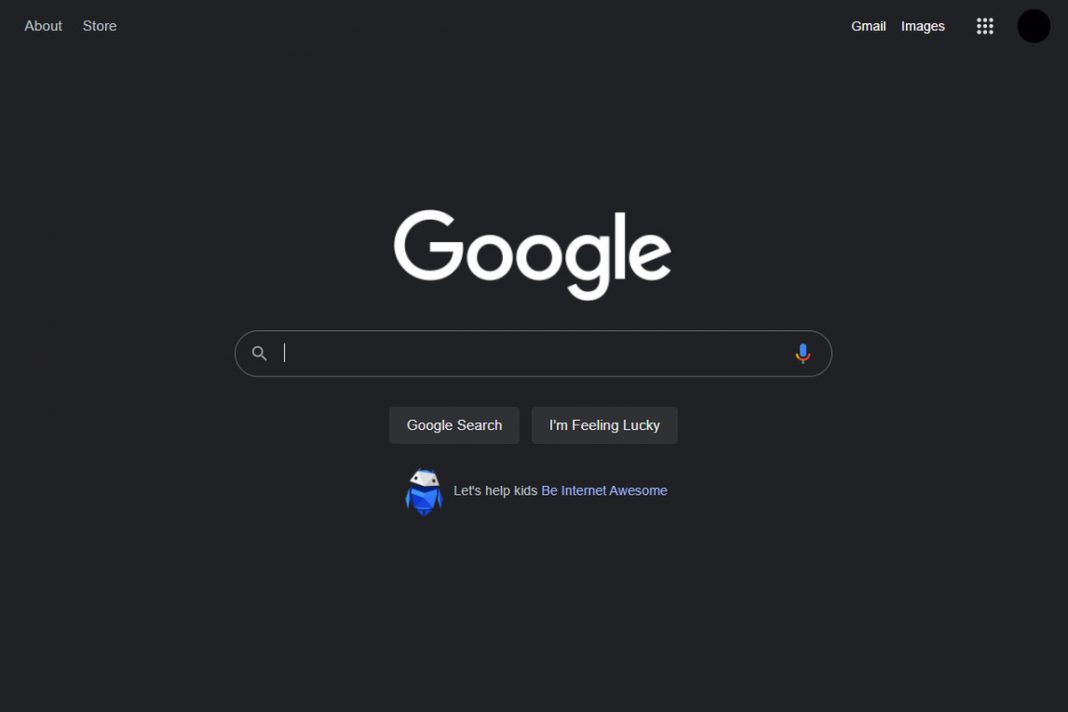
Here’s an example of what the dark mode looks like:

It’s unclear how widely the test has been rolled out. My search and several others online had the search pages automatically switch to dark mode, and 9to5Google and some people on Twitter have seen the new dark mode, too. But Google’s search pages are still white for me, even though I have dark mode turned on right now on macOS.
It’s also unclear if or when dark mode for desktop search might be officially rolled out more broadly. “We’re always testing new ways to improve our experience for our users, but don’t have anything specific to announce right now,” Google said in a statement to The Verge.
This isn’t the first time a desktop search dark mode has appeared: 9to5Google reported in January that some people were seeing dark mode then.
If you’re a dark mode fan, it’s been an eventful few days. Changes to Twitter’s dark mode caught some people unawares last week when their dark mode unexpectedly got even darker. And Microsoft is now testing changes to Word to make entire documents dark when you’re using dark mode.