In the second post of our series on cyber legislation and regulations, we will discuss the Cybersecurity Information Sharing Act (CISA) and its impact on organizations in the United States.
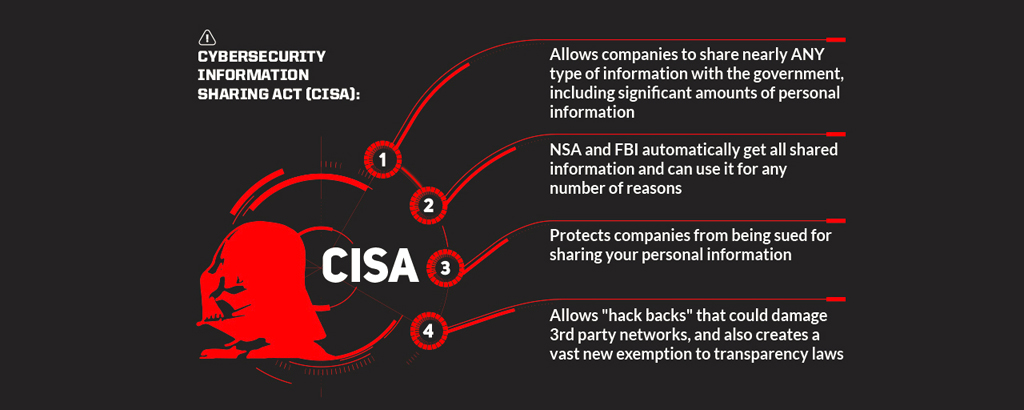
CISA is a law that was passed by the U.S. Congress in 2015 and aims to improve cybersecurity by encouraging the sharing of threat information between the government and the private sector. The law also includes provisions for protecting the privacy and civil liberties of individuals.
One of the key features of CISA is the establishment of Information Sharing and Analysis Organizations (ISAOs) which are intended to provide a secure platform for sharing cyber threat information among organizations. ISAOs are voluntary organizations that can be established by any private sector entity, including businesses, trade associations, and research institutions.
CISA also provides liability protection for organizations that share cyber threat information with the government and other organizations in good faith. This is intended to encourage organizations to share information without fear of legal repercussions.
CISA also requires the Department of Homeland Security (DHS) to establish guidelines and best practices for sharing cyber threat information, and to provide technical assistance to organizations that want to participate in information sharing.
The law also requires the DHS to establish a process for removing personal information from cyber threat information before it is shared. This is intended to protect the privacy and civil liberties of individuals.
CISA does not impose any specific cybersecurity requirements on organizations. Instead, it focuses on facilitating information sharing, and providing liability protection for organizations that share cyber threat information.
In summary, CISA is a law passed by the U.S Congress in 2015, which aims to improve cybersecurity by encouraging the sharing of threat information between the government and the private sector. The law establishes Information Sharing and Analysis Organizations, provides liability protection for organizations that share cyber threat information in good faith, and requires the Department of Homeland Security to establish guidelines and best practices for sharing cyber threat information. It also requires the DHS to establish a process for removing personal information before sharing cyber threat information.